Introduction:
One of the key aspects in managing the costs in cloud is to consume cloud native solutions and not to replicate the On-Premises components in cloud. A simple example is to use Azure Bastion host PaaS (Platform as A Service) instead of traditional RDP server farms for remote connectivity to Virtual machines in all possible scenarios.
Windows OS Patching is one of the key areas in managing application and infra servers. The Infra team spends lot of time in keeping the servers up to date with critical and security patches. With malwares and ransomware posing serious threat to various organizations, it is imperative for the SecOps team to track the patching updates for all the servers in the environment.
Traditionally System Center Configuration Manager (SCCM) servers were used to keep the virtual machines up to date. Extending the same to Azure environment shall be cumbersome and adds the cost of product and management as well.
Hence the solution of Azure Update Management …
Azure Update Management:
Microsoft Azure offers a free cloud native solution based on Azure automation for patch management of Windows and Linux Virtual Machines (VM) in cloud
Azure Update Management helps to manage operating system updates for the Windows and Linux virtual machines in Azure, physical or virtual machines in on-premises environments, and in other cloud environments.
We can quickly assess the status of available updates and manage the process of installing required updates for the virtual machines reporting to Update management.

Scenario:
One of the common project scenarios is that the customers having Azure virtual machines in both workgroup and domain environment due to various requirements. Often the workgroup VMs patching is difficult and could lead to low Azure Secure Score and hence posing the immediate challenge to act and remediate the VMs missing critical patches.
Extending On-Premises SCCM servers or WSUS is used in few organizations which adds up to management and cost overhead. Azure Update Management comes handy in such use cases.
Advantages of Azure Update Management:
- Works for both workgroup and domain joined VMs
- Supports Linux and Windows VMs
- Free of Cost
- Scheduled deployments with no reboot option
- Include or exclude selected patches with KB number
- Pre and post patching tasks using scripts
- Dashboard for easy reporting
- Option to install critical and security patches and all other patches in same or different schedules
Components in Azure Update Management:
- Azure Automation Account
- Log Analytics workspace
Azure Automation Account:
Azure Automation delivers a cloud-based automation and configuration service that supports consistent management across the Azure and non-Azure environments. It comprises process automation, configuration management, update management, shared capabilities and heterogenous features. Automation gives you complete control during deployment, operations and decommissioning of workloads and resources
Log Analytics Workspace:
Azure log analytics workspace is the logical storage unit where log data is collected and stored. It can be considered as the basic management unit of Azure monitor logs. It is used to collect data from various sources such as Azure Virtual machines, Windows or Linux virtual machines, Azure resources in a subscription etc.
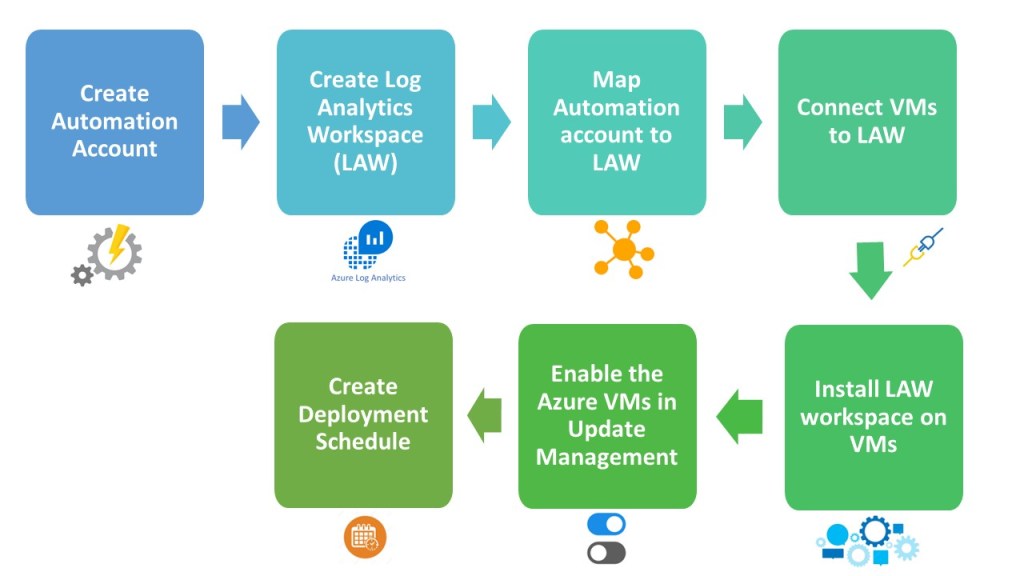
Implementation Workflow:
Supported Operating System:
Windows:
- Windows Server 2019 (Datacenter/Standard including Server Core)
- Windows Server 2016 (Datacenter/Standard excluding Server Core)
- Windows Server 2012 R2(Datacenter/Standard)
- Windows Server 2012
- Windows Server 2008 R2 (RTM and SP1 Standard)
Linux:
- CentOS 6, 7, and 8
- Oracle Linux 6.x, 7.x, 8x
- Red Hat Enterprise 6, 7, and 8
- SUSE Linux Enterprise Server 12, 15, and 15.1
- Ubuntu 14.04 LTS, 16.04 LTS, 18.04 LTS, and 20.04 LTS
Update Management does not support safely automating update management across all instances in an Azure virtual machine scale set. Automatic OS image upgrades is the recommended method for managing OS image upgrades on your scale set.
Step by Step Demo:
- The first step is to have an automation account. This account does NOT need any additional privilege such as “Run As” permission to update the OS of Azure VMs. We need to plan the deployment in such a way that the Automation account resides in the desired Azure region

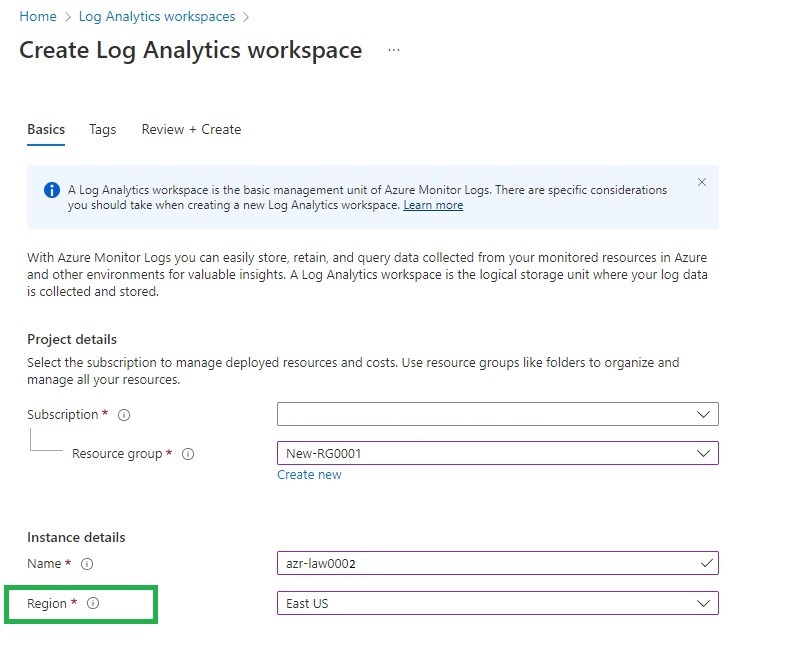
2. Then proceed with the creation of a Log Analytics workspace (LAW) account. The number of logs stored by the VMs in the LAW account is minimal and this is chargeable my Microsoft though update management is free. It is also very important to plan the same Azure region for the automation account and LAW account.
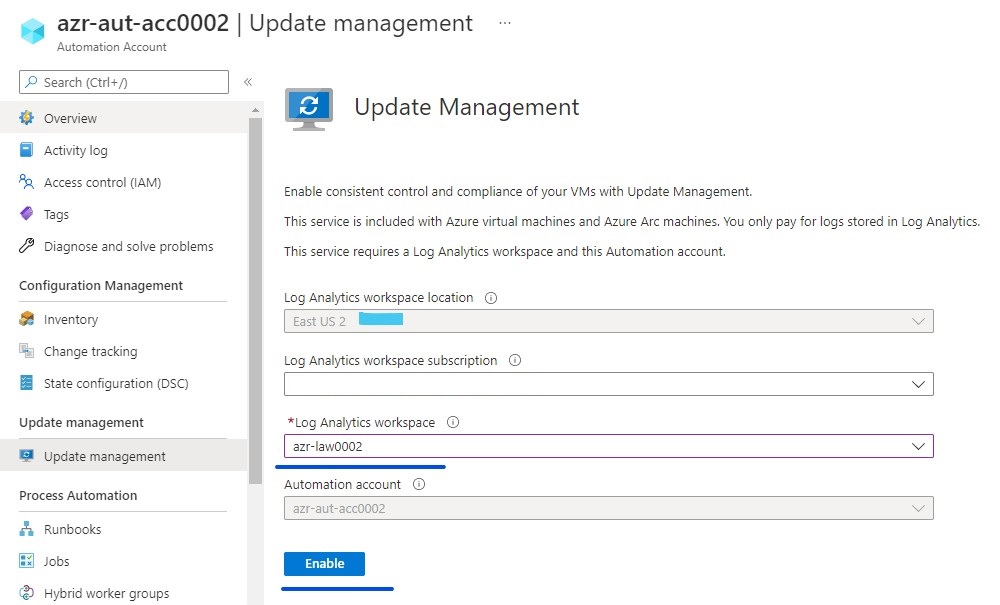
3. Then proceed with mapping the Automation Account to the Log analytics workspace account.
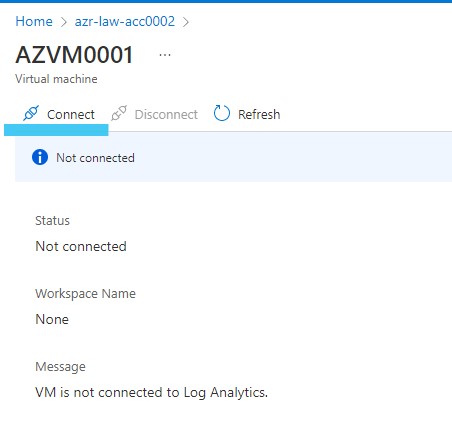
4. The next step is to connect the virtual machines to the log analytics workspace account. All the needed VMs and the automation account shall be connected to the same LAW account. Select the LAW account and then click on the VMs that need to be connected. This step can be automated using an Azure shell script.


5. All the VMs shall communicate with the LAW account with the help of LAW agent. The agent can be installed on the VMs manually or automated. In this case, we are using “Auto-Provisioning” option under Microsoft Defender for Cloud -> Environment Settings -> Setting

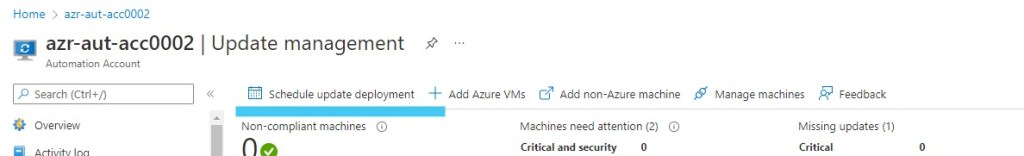
6. Now it is time to add the VMs into the Update Management section of the Automation account. Once added we can see the rich dashboard with information regarding the patching compliance and number of updates missing. However, this process shall take few hours and a VM which is shut down shall not report any data.



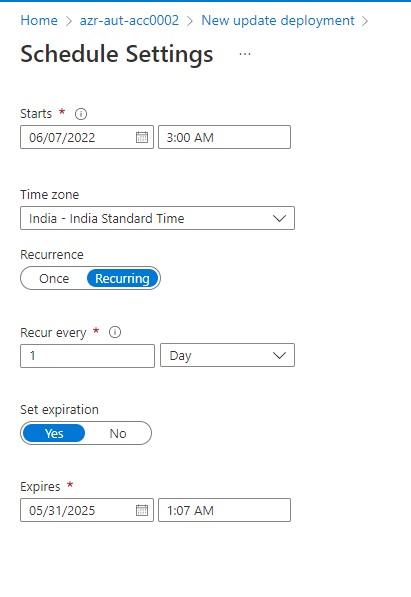
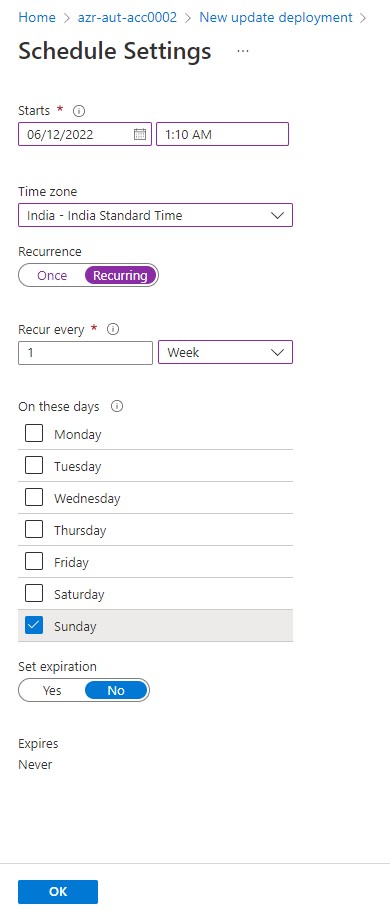
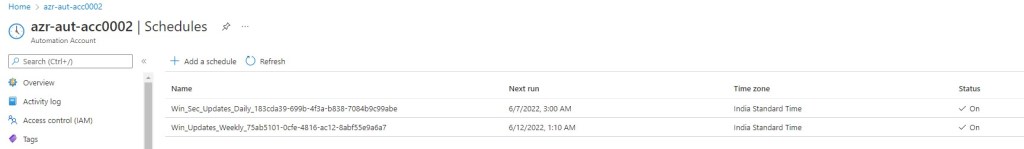
7. The last step is to create a deployment schedule as per the requirements. In my test case, I have a weekly recurring schedule for non-critical updates and daily recurring schedule for security patches and critical updates. The scheduling gives us a lot of flexibility to carry out pre and post patching tasks, include or exclude patches and the most important aspect of rebooting or no reboot of VMs post patching.




Thus we have covered the entire demo of a simple deployment of Azure Update Management. Apart from Azure Update Management, MS offers Azure VM Guest patching and Azure Update Center as the alternate and the upcoming options for patch management.
Links to refer:
https://docs.microsoft.com/en-us/azure/automation/update-management/overview
https://docs.microsoft.com/en-us/azure/virtual-machines/automatic-vm-guest-patching
Leave a comment